MX Deposit can be installed remotely in a matter of hours (not weeks) saving you time right from sign up. Start logging, managing, and collecting data immediately, with an intuitive system and step-by-step setup wizard.
Find the next world-class deposit with MX Deposit
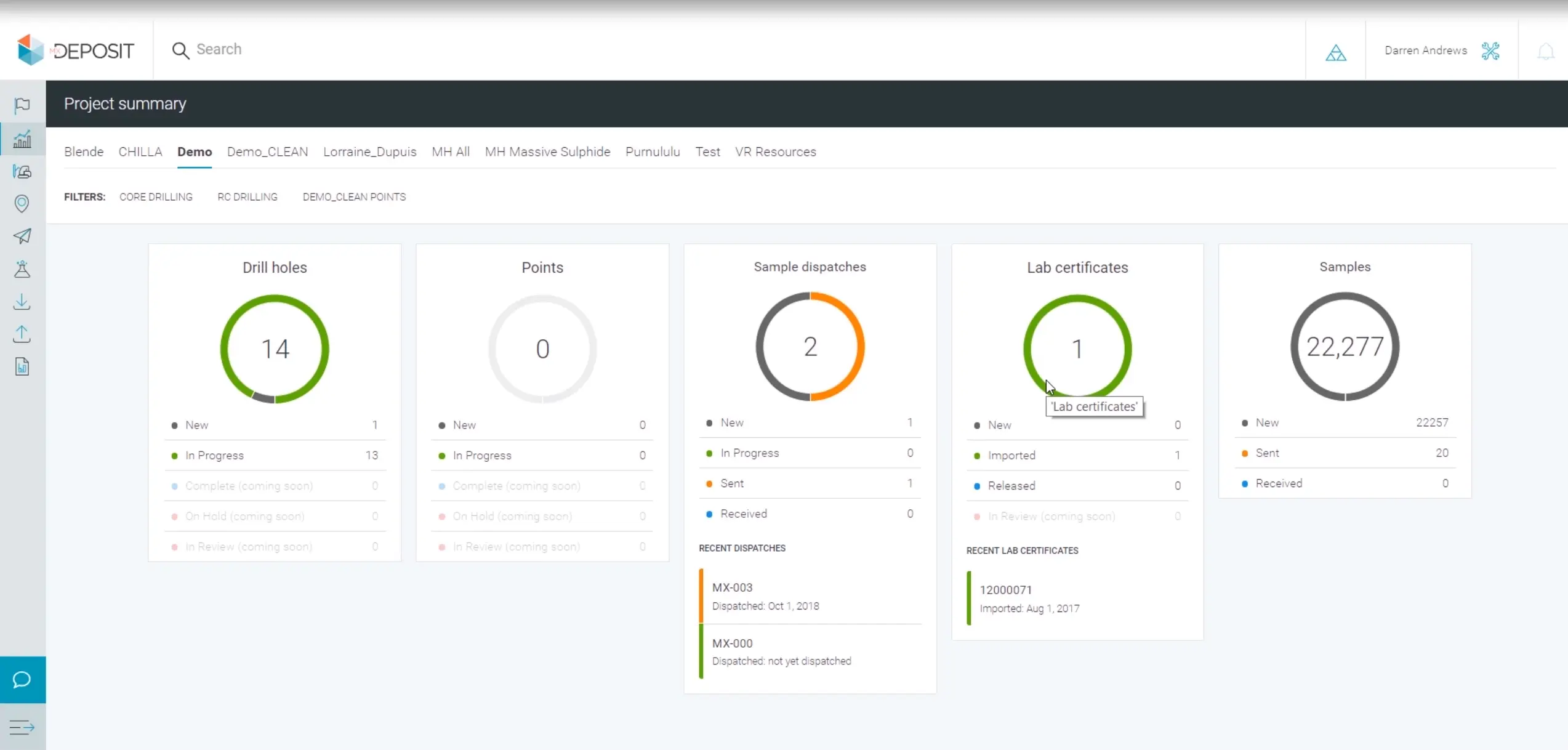
Collect, manage, share, and access your drillhole and sample data in the Cloud.
Get a demoTalk to usSave time from day one

Scale with your projects
It’s not fair to pay for what you don’t use and with MX Deposit you don’t have to. You only pay for when you need to use the software – select from monthly and annual subscriptions.
Stay agile in this changing market with an unlimited amount of drilling projects, a system that can be accessed from anywhere 24/7, and licences that can scale up for peak times or down once projects are complete.
Boost visibility and collaboration across teams
Bring all data into one single location. Users won’t need to flip between emails, text messages, files, or other sources to keep projects on track. See data updates, changes, and decisions made all in one location.
Everyone sees a single version of the truth in real-time and can collaborate with comments or questions harnessing your team’s collective power.

Build the solution for your situation
Customise your entire data management solution without a single line of code. MX Deposit lets you take control of your data by giving you the power to customise your data validation rules, import assays from any lab, and perform QA/QC while capturing a full audit trail on every piece of data.
Watch MX Deposit in action
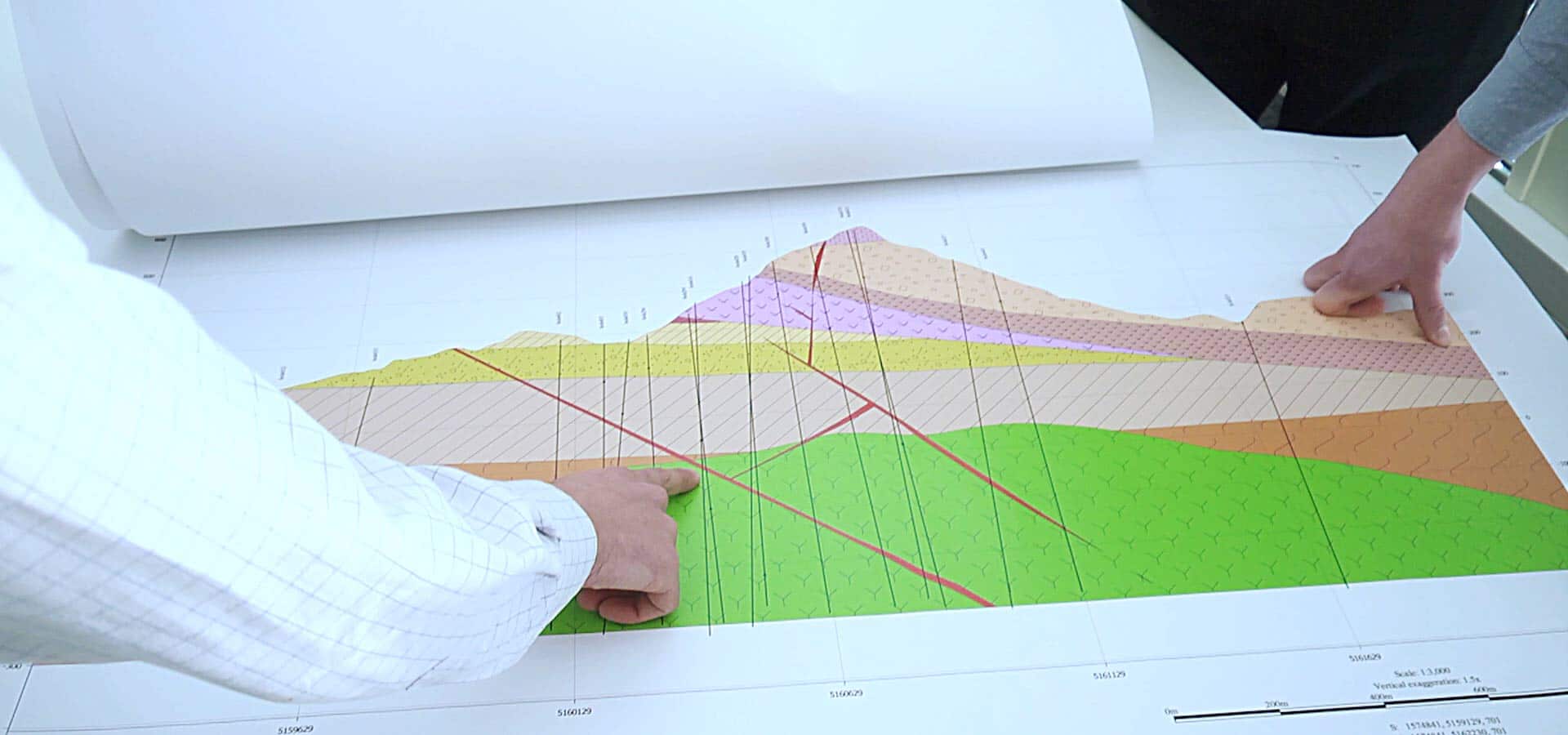
Simplify how drill hole and point sample data is collected, managed, and shared so geologists can make better decisions, faster – no matter where in the world they are.

Affordable, flexible, mobile, and hosted – take control over all of your drill hole and sample data
Get a demoWho uses MX Deposit?
Geological consultants
- Manage multiple customers simultaneously in one single location
- Improved confidence in your data with a clear audit trail of any and all changes
- Share selected projects with customers while maintaining privacy for other customer data
Juniors
- Get set up in a matter of hours not weeks
- Enterprise quality data management that’s affordable
- Avoid delays with powerful software that’s simple and easy to use
- Collaborate in real-time with your team, from wherever you are
- Flexibility to update your subscription type based on your situation
Majors
- Effectively manage multiple juniors all in the same instance
- Scale up or down in licences or licence types depending on their project status at any time
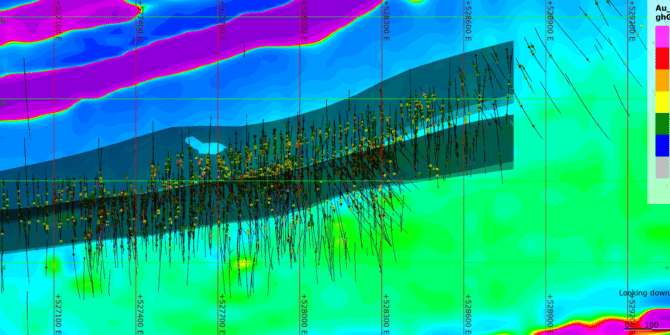
- Connect MX Deposit with Leapfrog Geo to visualise your geological data
- Open API for streamlined integration with existing or new systems
Mid-tiers
- Quickly set up users and projects for an agile exploration approach
- Maxmise profitability with monthly or annual cloud subscription options
- Innovative technology that lets you customise your entire data management
- Increase confidence by building your own data validation rules
Better data management at any stage of your mining project

An intuitive interface
Get your teams up to speed with MX Deposit quick with its step-by-step training wizard.
The intuitive interface means users can learn the fundamentals in just a few days without the need for onsite training so they can focus on managing data faster.
Full audit history
Keeping a detailed audit trail history is crucial to the confidence in your data.
MX Deposit automatically stores a clear and comprehensive audit trail which is useful when sharing your data for investment or when managing multiple projects.
Central communication
Break down silos across teams.
The real-time activity feed allows team members to post comments globally or to a specific group of people. Tag images and comments to specific drill holes, samples, tables, records, or values within a record.
Add on resource estimation extension Leapfrog Edge to carry out robust resource estimates.
Integrations
Our public API gives you the option to connect to the solution of your choice.
Gain intelligent insights and make even better decisions by delivering your drill hole information in 3D through Seequent’s Target for ArcGIS Pro.
Cloud hosted flexibility
Create an unlimited number of projects, drill holes, or samples and the freedom to scale up or down in your subscription numbers when it suits you.
Servers, security, and updates are automated so you always have the latest features and functionality.
Safe and secure
Data security is taken very seriously. There are several layers of enterprise-grade security built into the MX Deposit product, platform, and processes.
Communication is encrypted between all app components and connections so your data stays secure.
See why MX Deposit is the next generation data management solution for mining and exploration industries:
MX Success Stories
Better manage your data with a powerful workflow designed for exploration success

One source of truth with MX Deposit

MX Deposit & Imago logging and capture in action
Data Management Consultants

Expedio
Expedio is a consultancy specialising in geo-scientific information management since 1999. A well-designed data handling solution ensures maximum efficiency with minimum frustration, reducing timeframes, driving down costs and increasing productivity.
We solve data problems for junior explorers through to major miners, empowering confident decision making with always accurate data.

Orix Geoscience
Orix Geoscience is a Canadian geological consulting firm advancing strategic exploration and mining through the integration of data and innovative geological understanding.
Specialized services to meet client milestones include, document/map scanning, georeferencing/digitizing, data analysis, regional/property scale 2D GIS compilations, database migration, interpretation, 3D modelling, target generation, and executing field programs.
PrimeEarth
PrimeEarth Geoscience specialises in the management, integration, and governance of geoscientific observation data with the aim to build trust into your most important asset, the database.
We offer general support for the MX Deposit system including, data migrations, configuration of lists, tables, and activities, systems integration and establishing reporting workflows.
Useful Information
System Requirements
We recommend you use Windows 10, with a reasonably fast processor, mid range graphics and 32GB of system memory.
Supported Data/Formats
Supported kinds of data and formats that you can use with MX Deposit